Note:
The Funtoo Linux project has transitioned to "Hobby Mode" and this wiki is now read-only.
Difference between revisions of "Encrypted funtoo on linode"
Jump to navigation
Jump to search
Knightgats (talk | contribs) |
|||
| Line 121: | Line 121: | ||
[*] Initial RAM filesystem and RAM disk (initramfs/initrd) support | [*] Initial RAM filesystem and RAM disk (initramfs/initrd) support | ||
[*] Support initial ramdisks compressed using gzip | [*] Support initial ramdisks compressed using gzip | ||
}} | }} | ||
{{kernelop | {{kernelop | ||
Revision as of 15:55, January 18, 2017
This howto describes how to setup a complete Funtoo Encrypted Install ( Root File System and SWAP ) using LUKS and LVM on LINODE VPS
Setting Linode
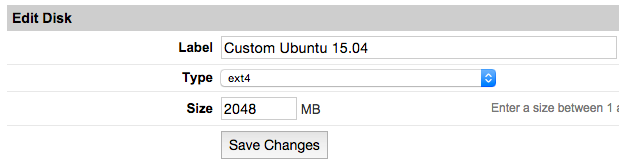
- From Linode Manager create a new Linode. Under the Disks section of the Linode Dashboard, click on "Create a new Disk:"
- Label your new disk image and choose an appropriate size. Here we will create "two disks" the first for root partition and another for swap. Set appropriate size for each one.
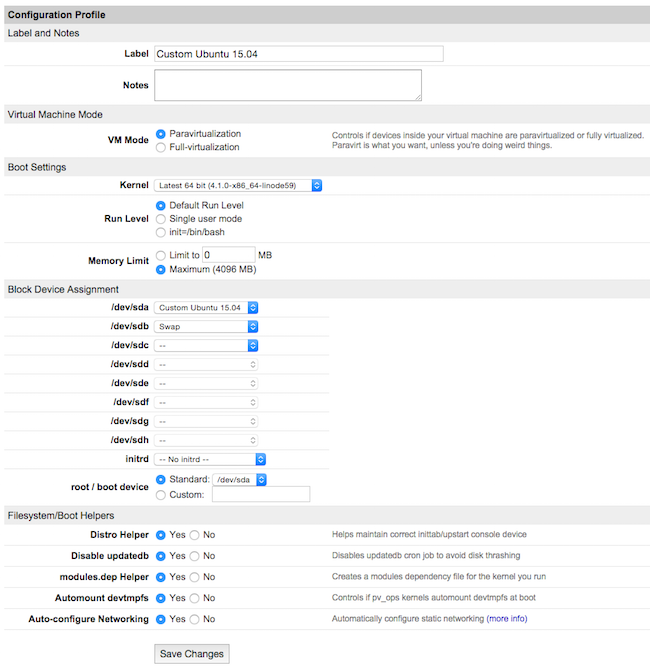
- Select the Create a New Configuration Profile option. Assign a label, and select your disk images under Block Device Assignment.
Click on Save Changes once your profile is complete.
- Return to the Linode DashBoard, and select the Rescue tab. From there, click the Reboot Into Rescue Mode button. Your Linode will now boot into the Finnix recovery image. Use the Lish shell to access your Linode.
- Run the following set of commands to create a root password and enable SSH server:
root # passwd ↵ root # service ssh start ↵
{{{title}}}
{{{body}}}
Note
Use Funtoo Install Guide for Reference.
- MBR Partition layout
Device Boot Start End Sectors Size Id Type /dev/sda1 * 2048 206847 204800 100M 83 Linux /dev/sda2 206848 48021503 47814656 22.8G 83 Linux
Device Boot Start End Sectors Size Id Type /dev/sdb1 2048 2318335 2316288 1.1G 83 Linux
- Encrypting Partitions ( root /dev/sda2 and swap /dev/sdb1 )
root # cryptsetup --cipher aes-xts-plain64 --hash sha512 --key-size 256 luksFormat /dev/sda2 ↵ root # cryptsetup --cipher aes-xts-plain64 --hash sha512 --key-size 256 luksFormat /dev/sdb1 ↵
- Initializing Encrypted Partitions
root # cryptsetup luksOpen /dev/sda2 cryptroot ↵ root # cryptsetup luksOpen /dev/sdb1 cryptswap ↵
- Creating Logical Volumes
root # pvcreate /dev/mapper/cryptroot ↵ root # vgcreate data /dev/mapper/cryptroot ↵ root # lvcreate -l 100%FREE -nroot data ↵
root # pvcreate /dev/mapper/cryptswap ↵ root # vgcreate cswap /dev/mapper/cryptswap ↵ root # lvcreate -l 100%FREE -nswap cswap ↵
- Creating FileSystems and Mounting them
root # mkfs.ext2 /dev/sda1 ↵ root # mkswap /dev/mapper/cswap-swap ↵ root # mkfs.ext4 /dev/mapper/data-root ↵ root # swapon /dev/mapper/cswap-swap ↵ root # mkdir /mnt/funtoo ↵ root # mount /dev/mapper/data-root /mnt/funtoo ↵ root # mkdir /mnt/funtoo/boot ↵ root # mount /dev/sda1 /mnt/funtoo/boot ↵
- Install the Stage 3 tarball and chroot
/etc/fstab # <fs> <mountpoint> <type> <opts> <dump/pass>
/dev/sda1 /boot ext2 noauto,noatime 1 2
/dev/mapper/cswap-swap none swap sw 0 0
/dev/mapper/data-root / ext4 noatime,nodiratime,defaults 0 1
- Update the System
root # echo "sys-kernel/debian-sources -binary" >> /etc/portage/package.use ↵ root # emerge -uDavN @world
- Building the kernel
Note
This step is very important
root # cd /usr/src/linux ↵ root # make menuconfig ↵
General setup --->
[*] Initial RAM filesystem and RAM disk (initramfs/initrd) support
[*] Support initial ramdisks compressed using gzip
Device Drivers --->
Generic Driver Options --->
[*] Maintain a devtmpfs filesystem to mount at /dev
Device Drivers --->
SCSI device support --->
{*} SCSI device support
<*> SCSI disk support
<*> SCSI generic support
[*] SCSI low-level drivers --->
<*> virtio-scsi support
[*] Multiple devices driver support --->
<*>Device Mapper Support
<*> Crypt target support
Virtio drivers --->
<*> PCI driver for virtio devices
[*] Support for legacy virtio draft 0.9.X and older devices
<*> Virtio balloon driver
<*> Virtio input driver
Cryptographic API --->
<*> XTS support
-*-AES cipher algorithms
<*> SHA256 digest algorithm (SSSE3/AVX/AVX2/SHA-NI)
<*> SHA512 digest algorithm (SSSE3/AVX/AVX2)
- Install GRUB2 and boot-update ebuild
/etc/boot.conf boot {
generate grub
default "Funtoo Linux"
timeout 3
}
"Funtoo Linux" {
kernel vmlinuz[-v]
initrd initramfs.cpio.gz
}
"Funtoo Linux genkernel" {
kernel kernel[-v]
initrd initramfs[-v]
params += enc_root=/dev/sda2 lvm luks root=/dev/mapper/data-root rootfstype=ext4 quiet
}
- Better-Initramfs
- Check if cryptsetup and lvm ebuilds are installed if not emerge them
- Configuring Swap to be mounted during boot
The key file will be stored on encrypted file system
root # dd bs=512 count=4 if=/dev/urandom of=/etc/.swapkey iflag=fullblock root # cryptsetup luksAddKey /dev/sdb1 /etc/.swapkey
/etc/conf.d/dmcrypt target=cryptswap
source='/dev/sdb1'
key='/etc/.swapkey'
- Installing bootloader to MBR and adjusting some stuff
root # grub-install --target=i386-pc --no-floppy /dev/sda ↵ root # boot-update ↵ root # emerge rsyslog dnscrypt-proxy ↵ root # rc-update add rsyslog default ↵ root # rc-update add dnscrypt-proxy default ↵ root # rc-update add dmcrypt boot ↵ root # rc-update add lvm boot ↵ root # rc-update -u ↵
- Configuring Networking
- Get IP Addresses from Linode Manager Remote Access Tab
root # cd /etc/init.d ↵ root # ln -s netif.tmpl net.eth0 ↵
/etc/conf.d/net.eth0 template="interface"
ipaddrs="200.230.240.45/24 2001:948:7:7::140/64"
nameservers="127.0.0.1"
gateway="200.230.240.1"
gateway6='fe80::1'
Show time!
- From Linode Manager, On Dashboard tab click Shutdown and Edit Configuration Profile
- Boot Settings -> Set Kernel to Direct Disc
- Filesystem/Boot Helpers -> Disable ALL Helpers
Boot your Line