The Funtoo Linux project has transitioned to "Hobby Mode" and this wiki is now read-only.
Libvirt
Introduction
This guide aims to help Funtoo users configure and administrate KVM/Qemu using Libvirt along with the GUI front-end Virt-Manager.
An overview according to libvirt.org, the [libvirt] project:
- is a toolkit to manage virtualization platforms
- is accessible from C, Python, Perl, Java and more
- is licensed under open source licenses
- supports KVM, QEMU, Xen, Virtuozzo, VMWare ESX, LXC, BHyve and more
- targets Linux, FreeBSD, Windows and OS-X
- is used by many applications
Check for KVM hardware support
To use KVM, one will need to verify the processor supports Intel Vt-x or AMD-V technology and that the necessary virtualization features are enabled within the BIOS. The following command should reveal if your hardware has virtualization enabed:
$ LC_ALL=C lscpu | grep Virtualization
Kernel configuration
The default Funtoo kernel, "debian-sources", has the needed KVM virtualization and virtual networking features enabled by default and will not require any reconfiguration. Non debian-sources users will need to verify the necessary kernel features are turned on in order to run KVM virtual machines and use virtual networking.
Installing libvirt
Optionally build libvirt with policykit support which will allow non-root users to authenticate as root in order to manage VM's and will also allow members of the libvirt group to manage VM's without using the root password.
$ echo 'app-emulation/libvirt policykit' >> /etc/portage/package.use
For desktop VM usage, It is recommended to build app-emulation/qemu with spice support, (Qemu will be pulled-in by emerging libvirt), for improved graphical and audio performance, clipboard-sharing and directory-sharing.
$ echo 'app-emulation/qemu spice' >> /etc/portage/package.use
It will likely ask to make some USE flag changes to the file /etc/portage/package.use -- if the changes look good, go ahead and add the changes it needs in order to be emerged.
$ emerge -av libvirt
After libvirt is finished compiling, you will have installed libvirt and pulled-in all of its' necessary dependencies, such as app-emulation/qemu and also net-firewall/ebtables and net-dns/dnsmasq for the default NAT/DHCP networking.
Enabling the libvirtd service
Start the libvirtd service:
$ rc-service libvirtd start
Add the libvirtd service to the openrc default runlevel:
$ rc-update add libvirtd
Enabling the "default" libvirt NAT
Set the virsh net "default" (the default libvirt NAT) to be autostarted by libvirtd
$ virsh net-autostart default
Start the "default" virsh network
$ virsh net-start default
Restart the libvirtd service to ensure everything has taken effect.
$ rc-service libvirtd restart
You can verify the default NAT is up is up using ifconfig:
$ ifconfig
virbr0: flags=4099<UP,BROADCAST,MULTICAST> mtu 1500
inet 192.168.122.1 netmask 255.255.255.0 broadcast 192.168.122.255
ether 52:54:00:74:7a:ac txqueuelen 1000 (Ethernet)
RX packets 6 bytes 737 (737.0 B)
RX errors 0 dropped 5 overruns 0 frame 0
TX packets 0 bytes 0 (0.0 B)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
You may also notice the "default" libvirt NAT inserts its' own additional iptables rules automatically upon every libvirtd restart:
$ iptables -S
-A FORWARD -d 192.168.122.0/24 -o virbr0 -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT -A FORWARD -s 192.168.122.0/24 -i virbr0 -j ACCEPT -A FORWARD -i virbr0 -o virbr0 -j ACCEPT -A FORWARD -o virbr0 -j REJECT --reject-with icmp-port-unreachable -A FORWARD -i virbr0 -j REJECT --reject-with icmp-port-unreachable -A FORWARD -d 192.168.122.0/24 -o virbr0 -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT -A FORWARD -s 192.168.122.0/24 -i virbr0 -j ACCEPT -A FORWARD -i virbr0 -o virbr0 -j ACCEPT -A FORWARD -o virbr0 -j REJECT --reject-with icmp-port-unreachable -A FORWARD -i virbr0 -j REJECT --reject-with icmp-port-unreachable -A FORWARD -d 192.168.122.0/24 -o virbr0 -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT -A FORWARD -s 192.168.122.0/24 -i virbr0 -j ACCEPT -A FORWARD -i virbr0 -o virbr0 -j ACCEPT -A FORWARD -o virbr0 -j REJECT --reject-with icmp-port-unreachable -A FORWARD -i virbr0 -j REJECT --reject-with icmp-port-unreachable -A OUTPUT -o virbr0 -p udp -m udp --dport 68 -j ACCEPT -A OUTPUT -o virbr0 -p udp -m udp --dport 68 -j ACCEPT -A OUTPUT -o virbr0 -p udp -m udp --dport 68 -j ACCEPT
Most virsh commands require root privileges
Libvirt VM's are managed using the virsh cli tool and the GUI front-end Virt-Manager. Using these tools will require root privileges unless they are built with policykit support enabled.
As noted from man(1) virsh, Template:Quote
Running as root, here are some example virsh commands:
$ virsh list --all $ virsh start foo $ virsh destroy foo
If libvirt was built with polictykit support, non-root users can run the same example virsh commands by addressing qemu:///system and authenticating as root via policykit:
$ virsh --connect qemu:///system list --all $ virsh --connect qemu:///system start foo $ virsh --connect qemu:///system destroy foo
Passwordless, non-root VM administration
If libvirt was built with policykit support, you may want to add your user to the additional "libvirt" group in order to administrate Virtual Machines without authenticating as root. You will need log out and back in for these changes to take affect.
$ gpasswd -a $USER libvirt
Tell Qemu where the UEFI bios firmware is located
edit /etc/libvirt/qemu.conf and include the following contents:
nvram = [
"/usr/share/edk2-ovmf/OVMF_CODE.fd:/usr/share/edk2-ovmf/OVMF_VARS.fd"
]
Using Virt-Manager to create and configure VM templates
Libvirt VM Templates are configured using XML and it is strongly recommended to install Virt-Manager in order to ease the virtual machine creation and configuration process. It may also be desirable to revisit the "virsh" commands later on, as it may be necessary to use them in order to make some advanced changes to XML templates that are not shown in the GUI Virt-Manager application.
Make sure the "gtk" use flag is enabled for Virt-Mananger, as it is a graphical application, and also "polictykit" unless you plan to run it as root, and then begin the emerge process:
echo 'app-emulation/virt-manager gtk policykit' >> /etc/portage/package.use
emerge -av virt-manager
Once again it is likely to need further USE flag changes in /etc/portage/package.use -- if the changes look good, go ahead and add the changes it needs in order to be emerged.
At this point of the guide, VM creation and administration should be relatively intuitive using the Virt-Manager GUI tool. What follows will be screenshots and guidelines for creating a Windows 10 Virtual Machine using Virt-Manager and the additional spice guest drivers:
Creating a new Virtual Machine Template
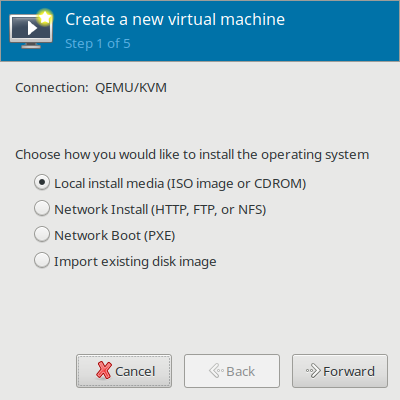
Click on File > New Virtual Machine > Local install media (ISO image or CDROM) > select "Forward"
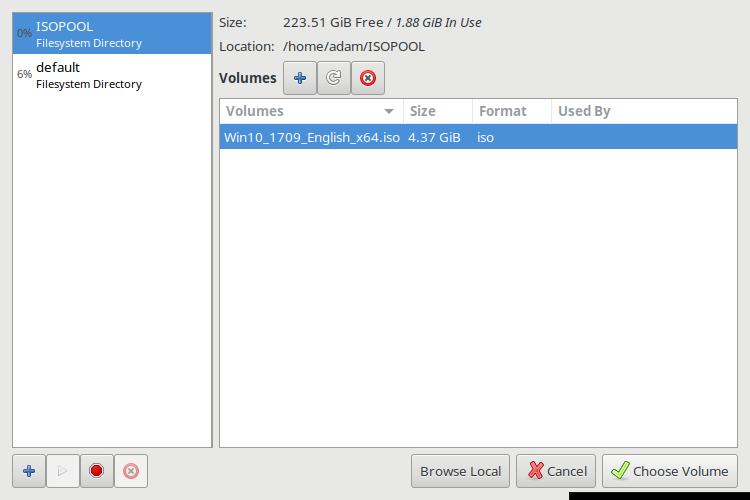
On your first use of Virt-Manager, while browsing to find your ISO image, you also should create a dedicated ISO "pool" which will be a directory on your filesystem where you can store all of your ISO files. Select the + to Add pool. After creating the ISO pool and moving your ISO images into the directory, then you can refresh it and browse for your ISO image in your ISO pool to use for the virtual machine install.
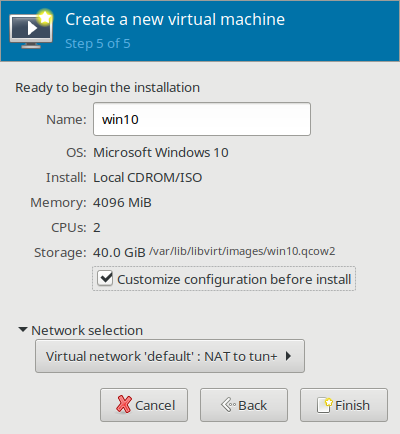
Customize Configuration Before Install
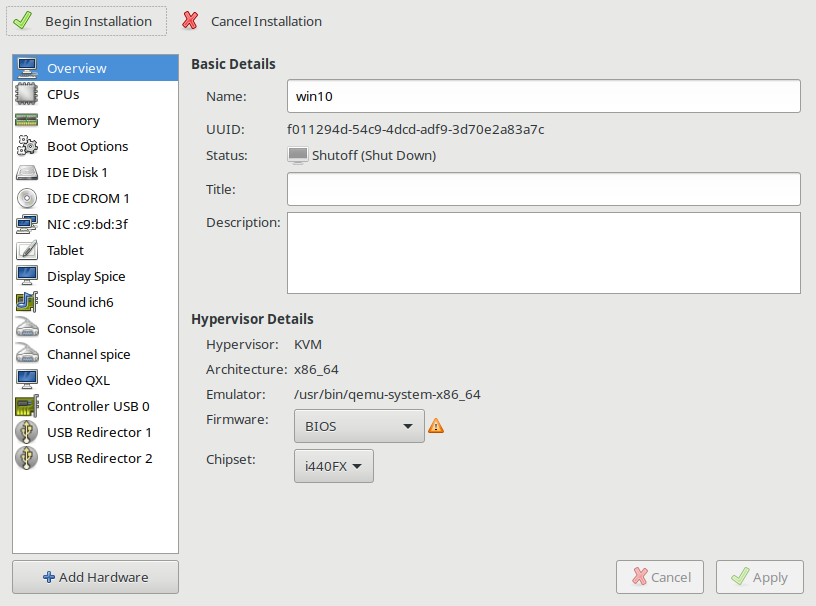
During the last step of VM template creation, it is a good idea to check the box "Customize Configuration Before Install" because that will allow you to choose which bios firmware will be used, which is an important feature that can only be configured once per template. After you choose a bios template on the next screen, you will be unable to change bios' without starting the process all over again.
The default is to use seabios, which is a legacy bios. OVMF (a uefi bios) is also available. When deciding on a chipset, i440FX is for emulation of older BIOS chipsets, and Q35 is for emulation of newer BIOS chipsets. After you select these options and choose "begin installation", there is no going back without creating a new template from scratch It is recommended to keep things simple and use the legacy seabios unless you have a reason to need the UEFI bios (like for pci-passthrough) ...
Note: You can return to the customization menu at any time from the main Virt-Manager window by selecting the virtual machine in question and choosing "open" and then selecting from the dropdown menu via "View > Details" to reconfigure the VM's general options.
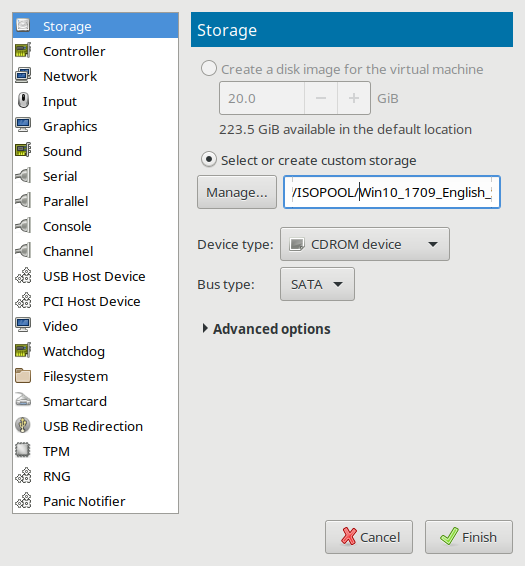
The Q35 BIOS will not work with IDE, so remove the IDE CDROM and IDE Storage and Select "Add Hardware" and add under "Storage" select SATA and add a new SATA CDROM and SATA storage device instead. It is also important to decide between using the "qcow2" format which allows for snapshotting with rollbacks/forwards and is additionally sparse provisioned, or to choose "raw" which will have none of these things, but may have better performance under some circumstances.
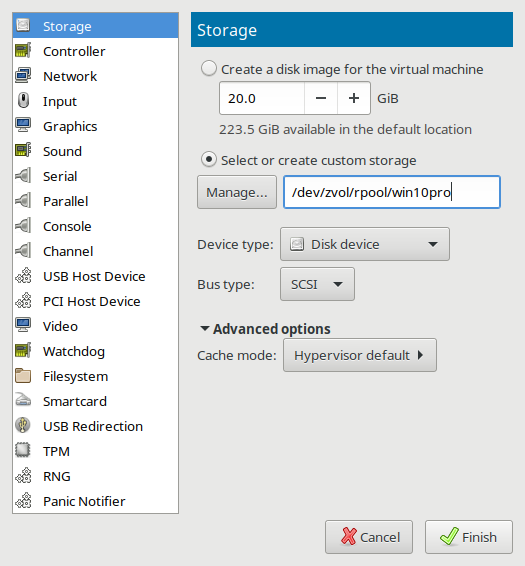
Note for ZFS users: While selecting Storage drives this is an excellent time to choose the disk "Device type" of "SCSI" which will use the Redhat passthrough "Virtio Scsi" disk controller for improved I/O performance, and you can create a sparse provisioned ZVOL with "zfs create -s -V 100G tank/VOLNAME" which can be addressed in this section of the Virt-Manager "Manage" textbox as "/dev/zvol/tank/VOLNAME". The virtio guest driver for taking advantage of the "Virtio Scsi" disk controller is included by default in Linux and FreeBSD kernels. Windows will be unable to see the Virtio Scsi storage disk and unable to install until you load the Redhat Virtio Scsi Driver during the Windows install process. (Windows installers include a menu with the ability to load drivers during the install process.) The RedHat Virtio Scsi driver for Windows is available to download as an ISO image.
Virt-Manager configures by default to offer the Spice server with QXL video and ich6 sound in addition to two USB redirectors and shared clipboard features enabled by default. These are all generally good things to have for desktop / graphical VM's, but depending on application, some users may opt to remove or change these devices away from defaults.
When you are ready to begin, choose "Begin Installation"
After successful installation of the OS, you still will probably want to install and enable the app-emulation/spice-vdagent service on every graphical guest machine. If it is a Windows guest machine, you can download a spice executeable from the official spice downloads page.
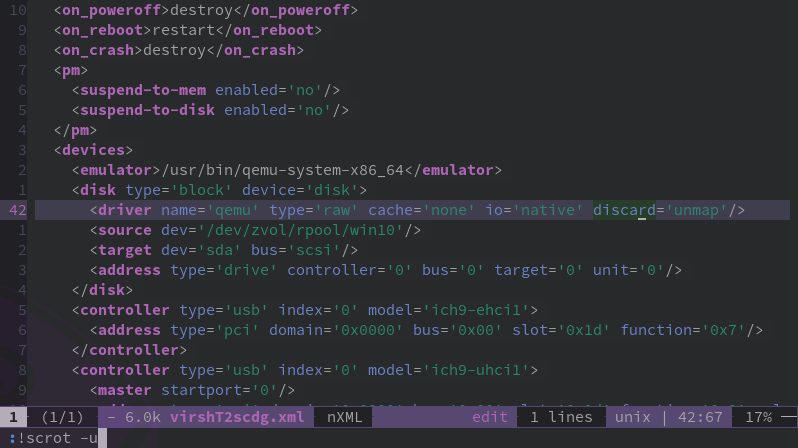
Advanced XML Template editing using virsh-edit
Some features are only able to be changed by editing the XML template directly. This example shows an XML template that was orginally generated using Virt-Manager, but by using the "virsh edit" command, has been modified on line 42 with the added parameter of discard='unmap' which allows a sparse provisioned windows VM's to trim the filesystem and return unused space back to a ZFS zpool.
Troubleshooting
Can't get beyond the bios screen after clicking "Begin Installation"? Be sure to check your devices are enabled and in the proper order in the "boot device order" section of the "boot options" if you're unable to get beyond the bios menu!
Project Links
- https://www.qemu.org
- https://www.linux-kvm.org
- https://libvirt.org
- https://virt-manager.org
- https://www.spice-space.org
=Resource Links
https://libvirt.org/docs.html https://wiki.archlinux.org/index.php/Libvirt